URL shortening services have been around for a long time (TinyURL started back in 2002) but it wasn’t until Twitter started gaining momentum that they became widely popular. Now we have a TON of them, including the original TinyURL, Bit.ly, Is.gd, and many, many more.
We have all placed an enormous amount of trust in these services by using them to such a large extent. They offer a legitimate, highly useful service, but we should at least be aware of the flip side of the coin.
Inherent problems with URL shortening services
There are several inherent problems with the use of URL shortening service, especially the widespread use that has become common on the Web lately.
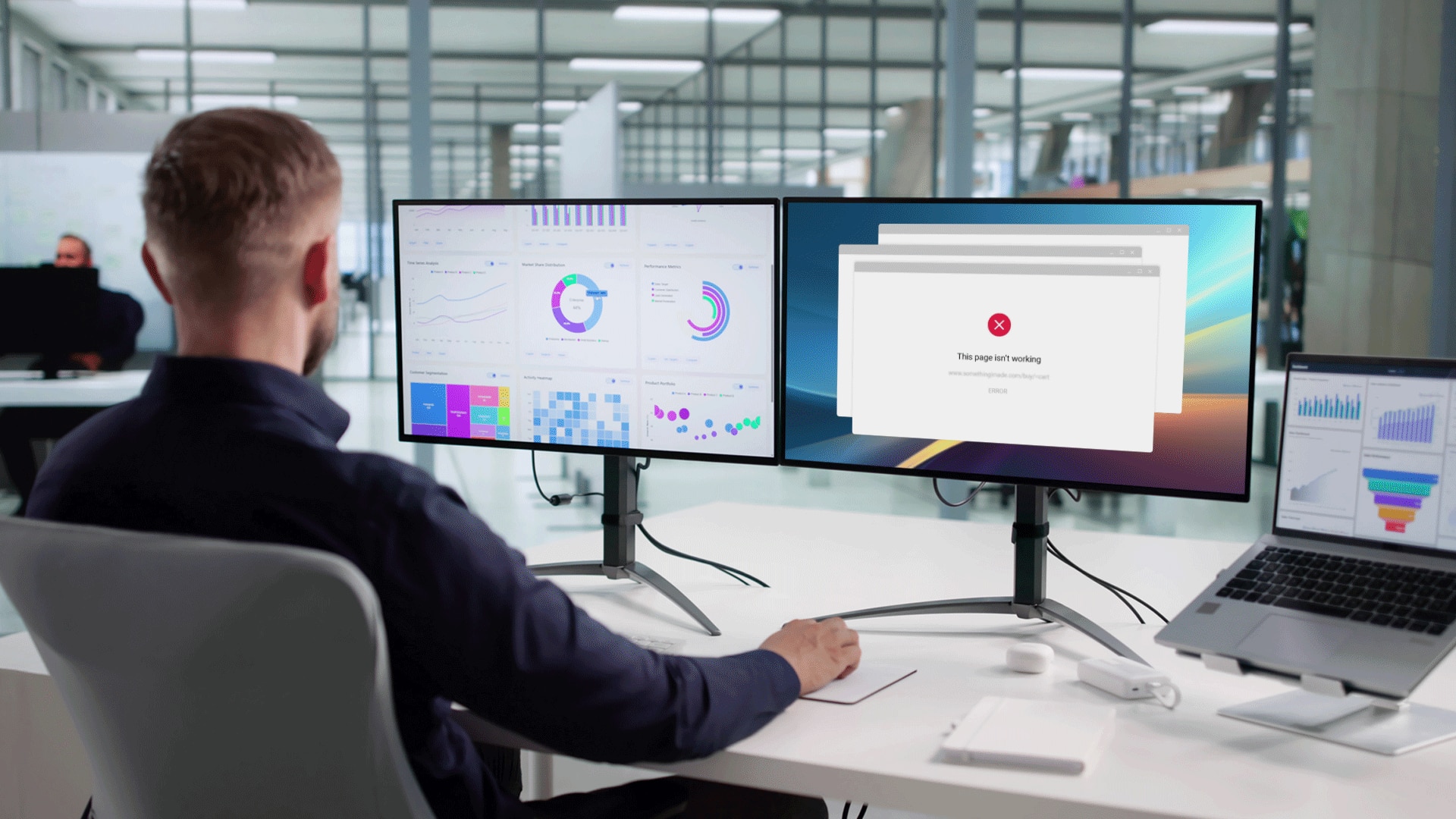
- It’s a middleman service that can break or cause slowdown. A URL shortening service acts as a middleman, redirecting you to the page that matches the shortened URL. Not only will that add overhead to how quickly you can access the target website, but if the service breaks you won’t be able to access the URL at all.
- What if the service disappears? If the service gets shut down for some reason, goes out of business, loses control of its domain name, or suffers from an irredeemable crash, your shortened URLs will never work again. (Although not a shortening service, remember how Del.icio.us competitor Ma.gnolia had to shut down after losing its data. These things do happen.)
- Hidden target link. You can’t look at a shortened URL and see where it leads which makes them popular for spam links.
And of course, there is always this nightmare scenario, which is what we referred to in the headline of this article:
Worst-case scenario, a hacked URL shortening service
Imagine if an enterprising hacker manages to compromise the URL shortening service you use (it’s happened). That hacker could potentially redirect ALL traffic going through the URL shortening service to whatever URL(s) he or she wants.
A compromised service could:
- Redirect you to websites with malicious code. You can end up being redirected to a web page with malware that could compromise your computer.
- Make you part of a DDoS attack. If all traffic (or a good part of it, especially for one of the larger services) is redirected to a specific target, the large amount of traffic would effectively become a DDoS attack on the target website.
Why we’ll keep using them anyway
In spite of everything we said in this article, URL shortening is a smart service, and in the era of Twitter pretty much a necessary one. You don’t want half of those 140 characters taken up by a long URL. Still, we suspect that it’s only a matter of time before one or more of the scenarios we have mentioned above become a reality. Hopefully we’re wrong. Knock on wood.
Photo by Ian Hampton.